Technology Due Diligence
Scalability | Cybersecurity | Intellectual Property | AI
Processed Due Diligence with adapted reports
Unique Source Code Scanning methodology
Team of experts covering all Tech topics, including AI
Technical Debt identification
Technology and business strategy alignment

They trust our Tech Due Diligence




























Reduce investment risks in IT with our Technology Due Diligence
Cybersecurity Risks
Cybersecurity Risks
• Data Theft
• Ransomware
• Opportunity Costs
• Reputational Consequences
• Reduced Efficiency
• Regulatory fines / Litigation
Intellectual Property Risks
Intellectual Property Risks
• Open Source Software Restrictions
• Loss of IP ownership
• Litigation
• Costs of coming into compliance
• Loss of asset value
Maintainability and Scalability Risks
Maintainability and Scalability Risks
• Re-engineering
• Increased development costs
• Delays in delivering functionality
• Decreased reliability
• High Technical Debt
What is included in our Technology Due Diligence

• Assessing human capital : we analyse the ability of the IT team to share knowledge and execute the technology roadmap
• Evaluating the full architecture and infrastructure: we ensure that these systems are secure, reliable, and scalable to support future growth
• Alignement with business strategy: we verify that the technology roadmap and investments have the potential to drive significant value

Effortless Tech Due Diligence: one dashboard, complete control

Sign in
Complete the Online Assessments

Upload the Source Code

Expert Contextualisation

Delivery of Risk Report and Action Plan


Tech DD Complete
100% secure, 100% of the time
We’ve been protecting source code for 40 years, always ensuring the highest levels of security.
• Secrecy of the source code assured through a strict workflow
• Upload made through secure server (no email, no SFTP) direclty through our plateform or via Git
• Temporary presence on our server with total deletion post-scan analysis
• No access by external parties or human ressources. Only scanner can read
• Non-disclosure agreements, letters of guarantee and certificate of destruction
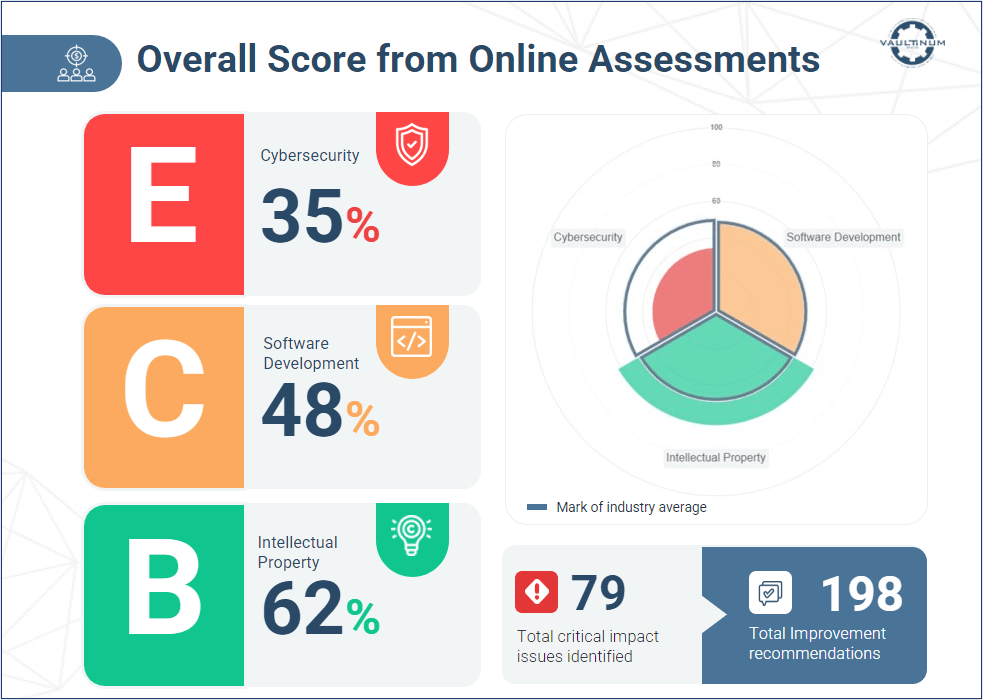
Online Assessment
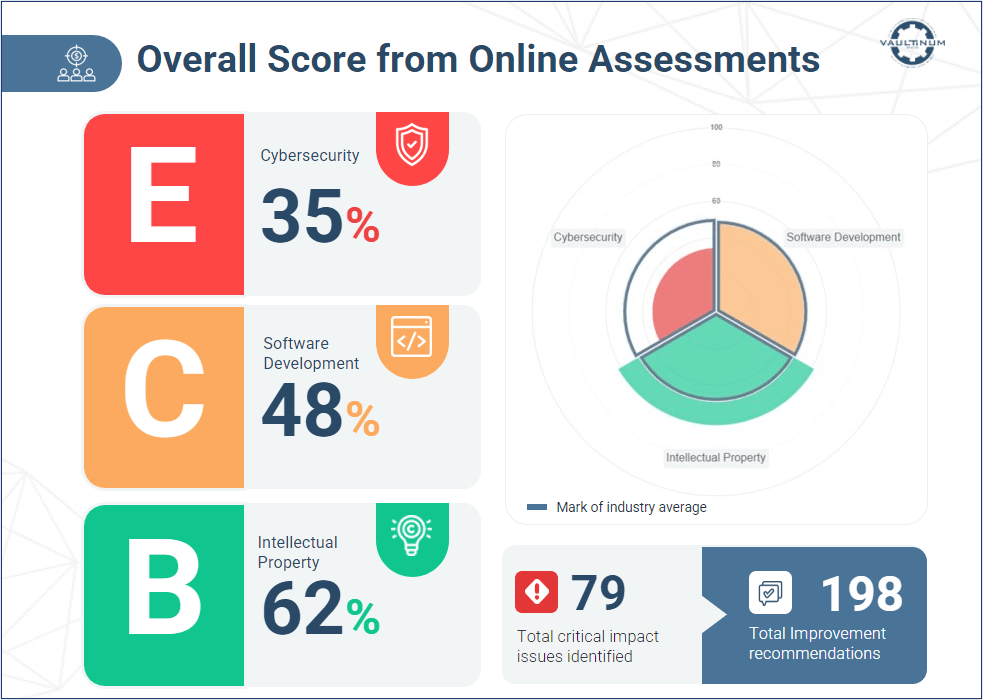
A series of online questionnaires to evaluate the audited organisation’s management of:
• Cybersecurity Practices
• Intellectual Property Protection
• Software Development
• IT infrastructure organisation
• GDPR processes
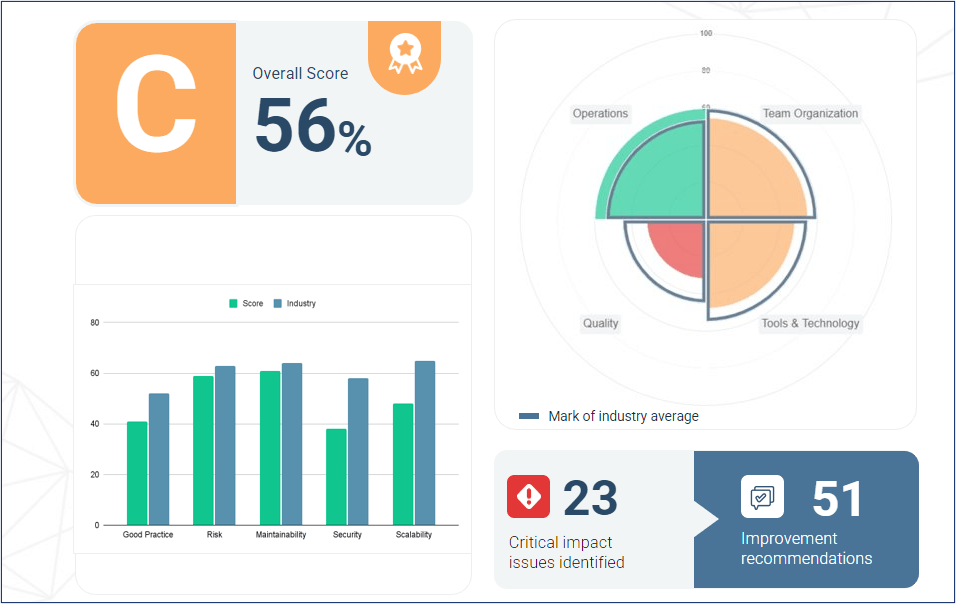
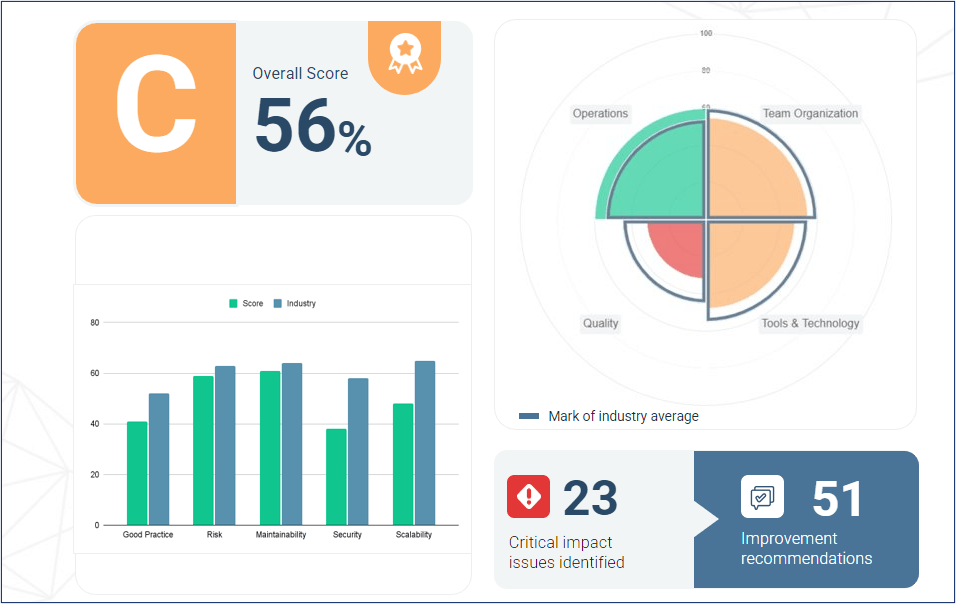
Source Code Scanning

Our unique proprietary source code scanning methodology gathers data analysis from 10 scanners, covering:
• Cyber vulnerabilities
• Code hygiene and maturity
• OSS dependencies
• OSS copy/paste
• OSS modifications
• Git analyzer for scalability...

Contextualisation with IT Experts

Following completion of the online assessments and code scan, an expert interview is carried out to:
• Review findings in the context of business objectives
• Identify mitigating factors
• Understand technology environment and end use
• Assess timelines to formulate action plan

Delivery of the Risk Report
In 3 weeks or less, Vaultinum will deliver a full risk report and action plan highlighting:
• Level of risk
• Scalability of the tech asset
• Cloud readiness
• Build up readiness
• OpEx and CapEx estimated risk
• Bottom-up analysis leading to better accuracy
• Deep tech background to factualize risks and recommendations
Do you want to know more about Tech Due Diligence at Vaultinum? We're here to answer your questions.
BOOK A MEETINGRelated articles


